What is Argon2? The Modern Standard for Password Hashing
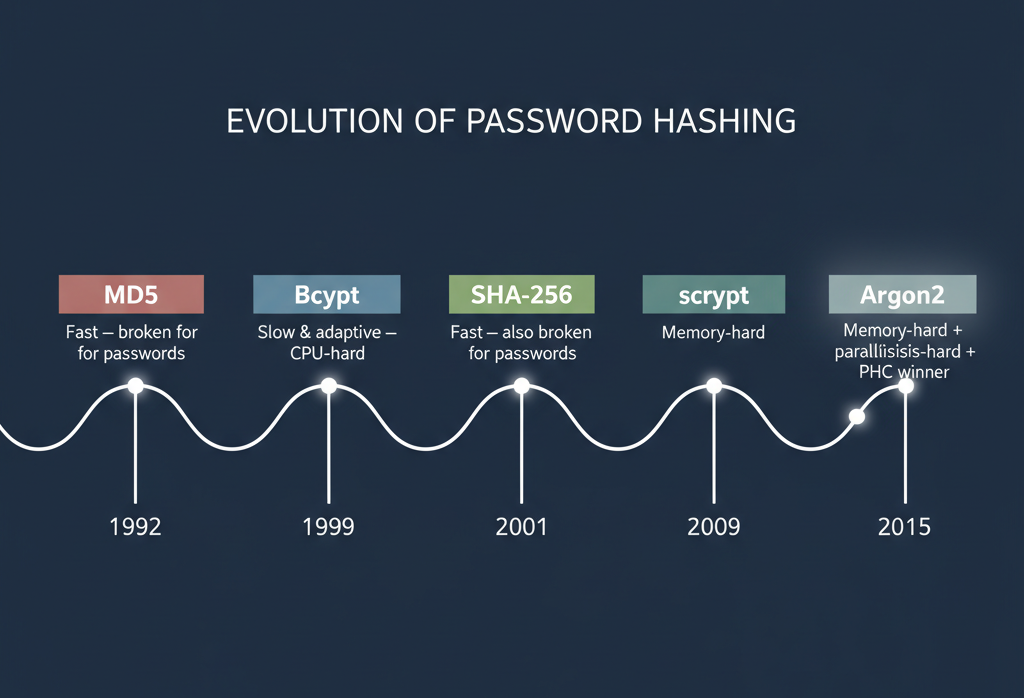
If you've read our articles on what hashing is and how Bcrypt works, you already understand the two fundamental rules of password security: you must never store passwords in plain text, and the hashing function you use must be deliberately slow to resist brute-force attacks.
For over two decades, Bcrypt was the gold standard for meeting those requirements. It introduced the concept of an adaptive cost factor — a dial you could turn to make the hash slower as hardware got faster. This was revolutionary in 1999, and Bcrypt remains a solid, well-tested choice today.
But the threat landscape continued to evolve. The rise of GPU-accelerated cracking tools and, more recently, specialized ASIC hardware created a new category of attack that Bcrypt wasn't designed to resist. The problem isn't that Bcrypt is "broken" — it's that it only consumes CPU time, and CPU time has become very cheap to buy in bulk.
This is the problem that Argon2 was built to solve.
What is Argon2?
Argon2 is a cryptographic key derivation function designed specifically for hashing passwords and deriving cryptographic keys. It was created by Alex Biryukov, Daniel Dinu, and Dmitry Khovratovich at the University of Luxembourg, and it won the Password Hashing Competition (PHC) in July 2015 — a rigorous, multi-year open process that evaluated dozens of candidate algorithms against real-world attack scenarios.
The core innovation of Argon2 over its predecessors is that it is memory-hard. While Bcrypt is CPU-hard (consuming processor cycles), Argon2 is specifically engineered to require a large, configurable amount of RAM during its computation. This distinction fundamentally changes the economics of attacking it.
Why does memory matter so much? A GPU or ASIC can have thousands of processing cores running in parallel. But RAM is expensive and physically large. By requiring a lot of memory, Argon2 ensures that an attacker cannot simply throw more cores at the problem. They need more RAM for every parallel attempt, and RAM costs money.
The Three Variants of Argon2
Argon2 comes in three flavors, each designed for a specific threat model. Understanding the differences is important for choosing the right one for your application.

Argon2d — Data-Dependent Memory Access
Uses a data-dependent memory access pattern, which maximizes resistance against GPU and ASIC cracking attacks. However, this pattern theoretically makes it susceptible to side-channel attacks. Best suited for applications where side-channel attacks are not a realistic concern, such as cryptocurrency proof-of-work functions.
Argon2i — Data-Independent Memory Access
Uses a data-independent memory access pattern, which eliminates side-channel timing vulnerabilities. This makes it the correct choice when the code runs in an environment where an attacker might observe memory access patterns. Slightly more vulnerable to GPU attacks than Argon2d, but still far stronger than Bcrypt.
Argon2id — Hybrid (Recommended)
Combines both approaches: the first half of the memory pass uses data-independent access (for side-channel resistance), and the second half uses data-dependent access (for GPU resistance). This hybrid design gives the best practical security for the widest range of attack scenarios. It is the variant recommended by the OWASP Foundation and RFC 9106 for general-purpose password hashing.
✅ Our Recommendation: For virtually all web applications, APIs, and user authentication systems, use Argon2id. It is the variant we use in our online hash generator tool.
The Three Cost Parameters
Like Bcrypt's cost factor, Argon2 gives you levers to tune how expensive each hash operation is. But instead of one dial, Argon2 gives you three.
1. Memory Cost (m)
This parameter controls how much RAM Argon2 allocates during the hashing operation, specified in kilobytes. A value of 65536 means the function will allocate and fill 64 MB of memory for every single hash.
2. Time Cost (t)
This controls the number of passes Argon2 makes over the memory block. More passes means more time spent computing. It's roughly analogous to Bcrypt's cost factor.
3. Parallelism (p)
This specifies how many independent memory lanes and threads Argon2 can use. Setting this to match the number of CPU cores available allows you to use your server's processing power more efficiently.
Argon2 vs. Bcrypt vs. scrypt: A Direct Comparison
| Property | Bcrypt | scrypt | Argon2id |
|---|---|---|---|
| Deliberately slow | Yes | Yes | Yes |
| Automatic salting | Yes | Manual | Manual |
| Memory-hard | No | Yes | Yes |
| Parallelism control | No | Limited | Configurable |
| GPU resistance | Moderate | Good | Excellent |
| Side-channel resistance | Partial | Partial | Yes |
| Password length limit | 72 bytes | None | None |
| PHC winner / standardized | No | No | Yes (RFC 9106) |
Note on Bcrypt's 72-byte limit: Bcrypt truncates passwords longer than 72 bytes. In practice, this rarely affects real users, but it's a known limitation. Argon2 has no such restriction.
What an Argon2 Hash Looks Like
Like Bcrypt, Argon2 stores all the information needed for verification in a single, self-contained string.
$argon2id$v=19$m=65536,t=3,p=4$c29tZXJhbmRvbXNhbHQ$RdescudvJCsgt3ub+b+dWRWJTmaaJObGFrequently Asked Questions
Is Argon2 safe to use in production today?
Yes. Argon2 has been publicly scrutinized for over a decade, was formally standardized as RFC 9106 in 2021, and is recommended by OWASP and NIST. It is actively used by major security-focused projects.
Should I migrate my existing Bcrypt hashes to Argon2?
A direct, immediate migration is not necessary if your Bcrypt cost factor is current. The recommended approach is a gradual, transparent migration: at each successful user login, re-hash their password with Argon2 and replace the stored Bcrypt hash.
Is Argon2 available in browsers for client-side hashing?
Yes — WebAssembly builds of Argon2 are available and work in modern browsers. Our online tool on this site uses a WASM build of Argon2 precisely because we never want your input to leave your browser.
Conclusion: The Right Choice for New Systems
The history of password hashing is a history of the security community staying one step ahead of increasingly powerful adversaries. Argon2id represents the current state of the art: it is deliberately slow, memory-hard, parallelism-aware, resistant to side-channel attacks, and formally standardized. If you are building a new authentication system today, there is no technical reason to choose anything else.